In this episode, we talk with David Knoke, Professor of Sociology at the University of Minnesota. We discuss the uses and benefits of network analysis, drawing upon his work on terrorist networks.
Though podcasting is at the heart of our project, we also plan to publish our episodes in a book of edited transcripts, making them even more accessible to students and instructors. You can download the edited transcript here. We’d love to hear your feedback on the multi-delivery format, and plan to release even more of these written versions on the site.
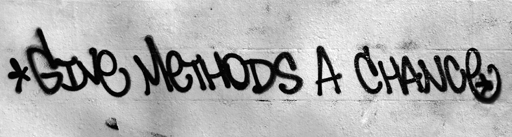
GMAC: We are here to talk about network analysis. If you were to introduce this method to an undergraduate class who had never heard of it, how would you describe it?
DK: If you go into a room full of people and ask how many people are “networkers,” they all raise their hand. They all know about Facebook and LinkedIn. So, intuitively, we all have a sense of social networks. We know who Mark Zuckerburg is. But, what most people don’t know is how to treat networking in a more systematic fashion. And this is what network analysis can do.
For instance, you can look at centrality of a network or do a core/periphery analysis. You can take a set of data and sort it by density clusters – high density, clustered folks who interact with each other, and then a periphery of folks who are less connected among themselves. There’s ego-centric networks, there’s complete networks, and there’s network change over time if you have longitudinal data.
There are many different foci. A classic example is a study of clique of women in the Mississippi Delta in the 1930’s. This study looked at a set of women who went to a series of parties. The question was, which women showed up at which parties? There was two modes: a set of folks, and a set of events.
What has most impressed me – and I’ve been doing this for close to 40 years – is how many different disciplines have been picking up network analysis. Anthropology and Sociology were there in the beginning, in the 1940s, but the real takeoff was the 1970s where a whole series of other disciplines begin to use it, such as Political Science. They even have an annual conference on network analysis. The students who take my course also come from a wide variety of disciplines, coming from departments you wouldn’t think of – like Forestry, Conservation Biology, and Rhetoric. It’s a real multi-disciplinary methodology.
We will use your recent research on terrorist networks as a way to understand how this method works. What were your central research questions?
This project is called “Three Modes of Al-Qaeda.” I ask, what are the lines of authority among a set of actors engaged in violent terrorist activities against Western targets?.
Instead of taking the narrative, historical approach of journalists, I formalized the study of Al-Qaeda by taking a network data collection approach. That meant reading a lot of online documents over a nearly twenty year span. I found 25 operations between 1992-2010 that had Western targets.
Podcast: Play in new window | Download