Sometimes it is worth it to follow a bad idea down, as far as it goes, and pull back up the contorted, gross, and contradictory thing that it has latched onto. That’s important because sometimes that bad idea is attached to a value or belief that you yourself hold. It’s just worth knowing what your values and beliefs are capable of, when applied in extreme degrees or to cases you would not necessarily apply them to. This week dozens of state governors and Republican presidential candidates have come out to say that they, even though they have no legal standing to do so, would not allow Syrian refugees into the states they govern. They usually couch their declarations in terms of risk evaluation. For example, Florida governor Rick Scott told reporters he couldn’t possibly let Syrians into the state “without an extensive evaluation of the risk these individuals may pose to our national security.” If we were to put aside the obvious –that this is nothing more than naked xenophobia dressed up as national security concern trolling– and draw out a cost benefit analysis, (the only language bureaucracies understand) could we possibly find a suitable “good enough” scenario?
First we have to look at the current system that they claim is inadequate. From Slate,
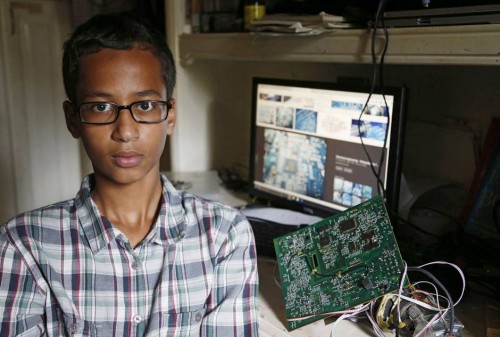
It takes anywhere from 18–24 months for a Syrian refugee to be cleared to live in the United States. First he or she must be registered with the U.N. High Commissioner for Refugees. This agency interviews refugees, conducts background checks, takes their biometric data, and establishes whether they belong to one of roughly 45 “categories of concern” given their past lives and work history in Syria. Typically, the applicants are women and children. If anything looks amiss, they are pulled from consideration. Then the U.S. government begins its own vetting. The applicants are interviewed again, and their names and particulars are run through terrorism databases. They receive additional screening when they arrive in the United States and then again after their first year in the country.
The US’s own vetting process requires crosschecks between the Departments of defense, state, and homeland security. Refugees’ names are compared to the ever-expanding and secret lists of terrorists that is maintained and checked by 19 intelligence and law-enforcement agencies. Once in the United States a recent immigrant is subject to all of the typical agencies that monitor and harass the poor, all the way down to local police. All of this, according to many elected officials, still presents unacceptable levels of risk.
If we are to come up with something better, we’ll have to find some sort of model security procedure and make the kind of crass cost-benefit comparison bureaucrats make all the time: How much are we willing to spend to protect future human life from potential terror threats? The U.S.’s Office of Management and Budget, since 2004, has told the rest of the federal government that they should value human life somewhere between one and ten million dollars. That fairly wide range is used to justify everything from the cost of FAA-mandated airplane part replacement schedules, to the methods the FDA requires for drug testing trials. The higher the “value of statistical life” (or VSL as it is called in actuarial circles), the more an agency is justified in demanding. It is no surprise then, that while the Environmental Protection Agency is busy defending its $7.4 million figure from loopholes, the department of defense is barely tethered to such a calculation.
Computing a VSL is fairly complicated but the general idea is fairly simple. The University of Pennsylvania’s law school maintains a blog on regulations (fun read) and describes VSL calculation this way:
When the purported goal of a new rule, such as one addressing worker safety or the environment, is to save lives, the federal Office of Information and Regulatory Affairs (OIRA) recommends measuring that rule’s benefits by using the value of a statistical life (VSL). OIRA defines the VSL as individuals’ “willingness to pay for reductions in risks of premature death.” For example, if people are willing to pay $10 to reduce their risk of death by one in a million, the VSL would be $10 million.
Statisticians back in 2012 claimed that after looking at the frequency and distribution of terror attacks since the 60s ”the likelihood of another 9/11 is between 20 and 50 per cent” by 2022. At the low range is an assumption of increased stability in the region, but we get closer to 50 per cent as power vacuums open up and resources like food and water get tight. If we were to assume that campaigns like the War on Terror help us increase stability (I don’t think this but plenty of government officials do and we are trying to stay internal to their own logic here) then how much more money do we need to add to what is already a $1.6 trillion price tag?
For the sake of argument lets use fiscal year 2008, the most expensive year of the War on Terror, as our VSL. That makes sense given that so many conservative politicians blame our relatively reduced military presence in the Middle East for the rise of ISIS and the whole point of the War on Terror (among other more abstract goals) is to prevent Americans from dying at the hands of terrorists. It also seems likely that any increased costs of screening refugees would get passed through defense spending so that such a system would avoid intentional government shutdowns and austerity measures. Despite the alramingly high probability of another major attack within a decade, the likelihood of an American dying from any kind of terrorist attack (and this includes domestic white supremacist terrorists!) is about 1 in 20 million. Presumably this is not good enough so lets say we wanted to decrease that likelihood to the level of bee and wasp sting deaths: approximately 25 million to 1. That would mean people would have to be willing to pay $39,000 to decrease odds that are already substantially lower than all assaults by firearms (24,974 in 1) or literally just walking (54,538 to 1).
Of course, just as we do not hand over a specific amount of money to the EPA for statistically-less-likely-to-kill-you air and water, no one will actually pay this $39,000 figure. Instead, it will be used to justify increased taxes and decreased spending in other departments. I will admit that, as a qualitative social scientist, I may have gotten this wrong but I am certainly in the ballpark. Even a trained economist who does these sorts of calculations for a living would have to add an asterisk about all of the factors that complicate their VSL calculations. The depreciating value of war machines, the relative effectiveness of any given campaign or program, and many other things could cause the VSL to rise or fall. In any case it is safe to say that given the high absolute price we have paid in the past for anti-terror tactics, and the relatively insignificant likelihood of dying in a terrorist attack, we are more than willing to spend ourselves to ruin. And this is precisely the stated, long-term tactic of non-state combatants. While terror is the existential weapon they wield, their blows always lead to a bleeding of money.
We tend to think of acts of terror as unique, discreet events that we might foil through gathering intelligence on specific plans carried out by identifiable individuals. Social scientists that study disasters and risk call these “discreet accidents” and, in the words of prominent disaster studies scholar Charles Perrow [paywall], casting accidents as discreet means that they can be prevented in the future by dissecting exactly what went wrong and correcting it. The 9/11 Commission report did just that: it pointed to a failure in intelligence sharing among several agencies and now those organizations circulate information more than ever before. But critics of that report, from presidential candidates to conspiracy theorists, continue to define 9/11 as a discreet accident: Someone is to blame, something went wrong, and ultimately 9/11 was preventable.
The terrifying truth is that politically motivated violence is inevitable given our present condition. Terrorism is what Perrow would call a “normal accident,” one that “emerges from the characteristics of the systems themselves.” Normal accidents are unavoidable not only because all human endeavors are prone to error (e.g. someone won’t catch the bomb in the suitcase or a crucial piece of intelligence won’t make it to the right desk in time), but also because the complexity of systems always produce an infinite combination of errors that are not recognizable as dangerous until the accident occurs. Perrow calls this “negative synergy” because the accident is always worse than the sum of the errors that produced it. The only solution Perrow provides is replacing complex, “tightly coupled” systems with decentralized “loosely coupled” systems so that when errors inevitably occur, they cannot spread, iterate, and produce a cascade effect that leads to disaster. This seems imminently applicable to things like electrical grids (e.g. smart grids of decentralized solar panels instead of nuclear power plants) but less imaginable when it comes to geopolitics. That is, of course, if you cannot fathom a world without borders.